
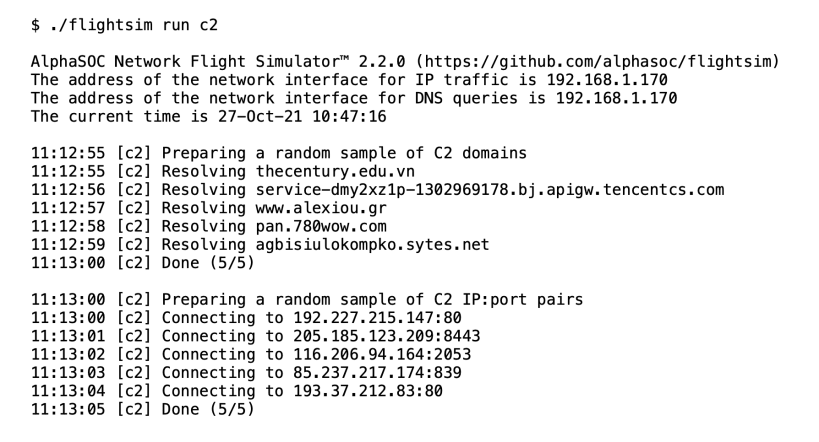
Instantly generate malicious network traffic patterns with flightsim to evaluate your security controls and threat detection stack. The utility performs tests to simulate DNS tunneling, DGA traffic, requests to known active C2 destinations, and other suspicious traffic patterns.
This recent blog post describes the flightsim utility and its various modules:
This snap hasn't been updated in a while. It might be unmaintained and have stability or security issues.
You are about to open
Do you wish to proceed?
Thank you for your report. Information you provided will help us investigate further.
There was an error while sending your report. Please try again later.
Snaps are applications packaged with all their dependencies to run on all popular Linux distributions from a single build. They update automatically and roll back gracefully.
Snaps are discoverable and installable from the Snap Store, an app store with an audience of millions.

Snap can be installed on Fedora from the command line:
sudo dnf install snapd
Either log out and back in again, or restart your system, to ensure snap’s paths are updated correctly.
To enable classic snap support, enter the following to create a symbolic link between /var/lib/snapd/snap and /snap:
sudo ln -s /var/lib/snapd/snap /snap
To install AlphaSOC flightsim, simply use the following command:
sudo snap install flightsim
Browse and find snaps from the convenience of your desktop using the snap store snap.

Interested to find out more about snaps? Want to publish your own application? Visit snapcraft.io now.